AI-Based Tactics for Advanced Network Deception
Overview
Modern computer networks have become highly connected and heterogeneous due to the integration of a diverse array of devices and protocols, including Internet of Things (IoT), robots, sensors, and other connected systems. This growing complexity and heterogeneity, although essential for providing sophisticated services and adapting to rapidly changing demands, also pose significant security challenges. Networks now encompass an increasing number of devices with different operating systems, making them more susceptible to interference, cyber attacks, and complex management issues such as patching vulnerabilities. These security concerns become even more critical in military environments, where the Internet of Battlefield Things (IoBT) necessitates the protection of critical nodes and system components. To counter cyber threats, network administrators, or defenders, often employ cyber deception techniques during the reconnaissance stage of an attack.

Under this project, we explore multiple network deception mechanisms. For example, In MirageNet project, we are introducing our vision for a GAN-based synthetic network traffic generation framework, which can automatically create synthetic network models of protocols, applications, and devices. With the potential to build many applications for privacy, security, and network optimization. As a first step towards this vision, we developed the MiragePkt framework that can automatically understand the syntax of the network packets from the raw network packets and then synthetically generate network packets. Figure 1 shows the overall architecture of the MiragePkt GAN model, which consists of two components: a generator and a discriminator. The generator’s objective is to generate the sequence of tokens representing the byte stream of a packet. The discriminator’s objective is to extract the features from the generated sequence and identify whether the generated sequence belongs to the true distribution of the training data.
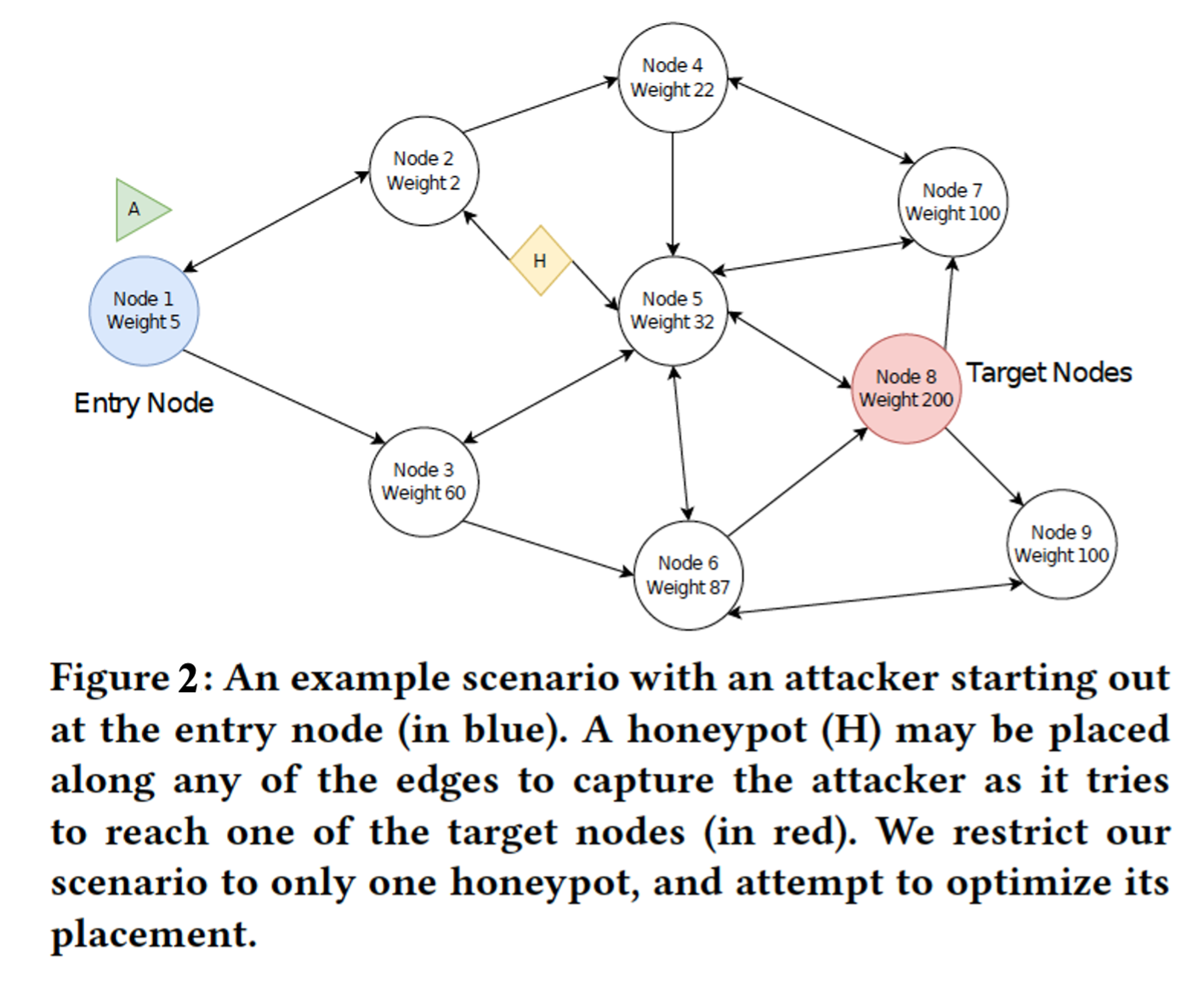
Another project we developed is about the strategic honeypot placement that is pivotal for enhanced network deception. In this project, we introduce a novel approach, leveraging Graph Neural Networks (GNNs), to optimize honeypot placements, outstripping traditional game-theoretic methods. Traditional techniques often face computational inefficiencies due to the "curse of dimensionality" in complex dynamic environments. Figure 2 shows a scenario in which the network is exposed to a single attacker, entering through a designated entry node. Our primary objective is to ascertain the most strategic edge within this network on which to deploy a honeypot. By doing so, we aim to maximize our chances of intercepting and neutralizing the attacker, thereby safeguarding the network’s integrity. Our GNN model, through extensive exploration of architectures including Graph Attention Transformers (GAT) and Graph Transformer models, showcases superior performance. With the integration of game-theoretic edge features, the model achieves a remarkable test accuracy of 92.34%. Additionally, our GNN solution provides a 139x inference speedup over classical methods, underpinning its efficiency and potential to revolutionize cybersecurity strategies.
Publications
- Santosh Kumar Nukavarapu, Mohammed Ayyat and Tamer Nadeem, "MirageNet - Towards a GAN-based Framework for Synthetic Network Traffic Generation," GLOBECOM 2022 - 2022 IEEE Global Communications Conference, Rio de Janeiro, Brazil, 2022, pp. 3089-3095, doi: 10.1109/GLOBECOM48099.2022.10001494.
-
Mohamed Osman, Tamer Nadeem, Ahmed Hemida, and Charles Kamhoua. 2023. Optimizing Honeypot Placement Strategies with Graph Neural Networks for Enhanced Resilience via Cyber Deception. In Proceedings of the 2nd on Graph Neural Networking Workshop 2023 (GNNet '23). Association for Computing Machinery, New York, NY, USA, 37–43. https://doi.org/10.1145/3630049.3630169
Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author(s) and do not necessarily reflect the views of the National Science Foundation.